This post will show you the steps necessary to configure Single Sign On with Active Directory Federation Services and UserVoice.
Overview
UserVoice is a powerful feedback and ticketing system that I’ve been integrating into SharePoint intranet portals lately. When used in an intranet scenario, having an integrated Single Sign On experience is critical to enable employees to submit feedback and issues, without having to login with a separate set of credentials. With the SAML 2.0 support of UserVoice, it’s easy to enable Single Sign On between UserVoice and your Active Directory Federation Services (ADFS) infrastructure. The official reference for SAML integration can be found here.
Configuring the Relying Party in ADFS
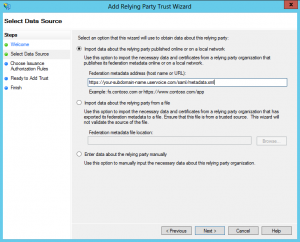
The first step to setting up SSO for UserVoice is to configure a Relying Party trust in ADFS. Fortunately this is made easy as UserVoice provides an autodiscovery url for federation metadata. Here are the steps to configure the RP:
- To start, open the ADFS 2.0 management console. Click on the link to Add Relying Party…
- In the Select Data Source screen of the wizard, enter the url to UserVoice’s metadata endpoint, similar to the following: https://your-subdomain-name.uservoice.com/saml/metadata.xml (Replace your-subdomain-name with the one given to you by UserVoice).
- Click through the Wizard, give your RP a name/description, and accept all other defaults.
- Select your new Relying Party in the Management Console, right-click, and choose Edit Claim Rules… Under Issuance Transform Rules, click Add Rule… and choose Send LDAP Attributes as Claims.
- UserVoice needs three claims named: 1) “email”, 2) “display_name”, and 3) “guid”. On the claim rule screen, configure it as shown in the screen below. You will have to manually type a few of these into the text boxes, rather than picking from the dropdown. E-Mail-Addresses (from dropdown) will map to “email” (hand-typed), Display-Name (from dropdown) will map to “display_name” (hand-typed), and “objectGUID” (hand-typed) will map to “guid” (hand-typed).
Configure SSO in UserVoice
Now that the Relying Party is configured in ADFS, the next step is to configure the SSO settings in UserVoice.
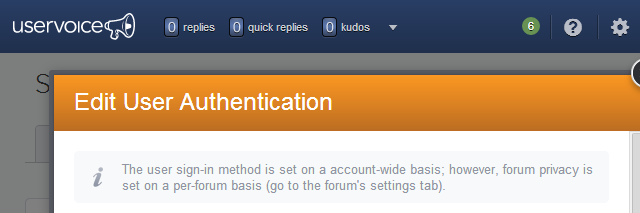
- Navigate to the admin interface in UserVoice, and click on Settings > Web Portal > User Authentication > Edit.
- Check the radio button for Single Sign-On.
- On the Edit screen, you will need to upload your Token Signing Certificate, exported from your ADFS server. You should see your certificate’s fingerprint after upload.
- Ignore the SSO Key field, as it is not used in SAML authentication.
- In the SSO Remote Sign-In field, enter a url in the following format: https://youradfsserverurl.com/adfs/ls/IdpInitiatedSignOn.aspx?loginToRp=your-subdomain-name.uservoice.com. For the loginToRp parameter, this is the identity of the Relying Party you configured in ADFS. This will be your UserVoice subdomain.
Testing
Once you’ve configured Single Sign On, navigate to the admin section of UserVoice with an In-Private or Incognito window (e.g. http://your-subdomain-name.uservoice.com/admin). In the login box, you should now see a globe icon and should be able to login via SSO when clicked:
Troubleshooting Errors
If you run into errors, look at the SSO logs from within the UserVoice Admin section. A common problem I encountered was an error regarding NotBefore token “Current time is earlier than NotBefore condition” (noted on the official SAML docs). This is due to a slight server-clock mismatch between your ADFS server and the UserVoice servers. To fix this, I had to adjust the NotBefore skew in ADFS via Powershell, to account for up to a 2 minute deviance in time:
|
1 |
Set-ADFSRelyingPartyTrust -TargetIdentifier "your-subdomain-name.uservoice.com" -NotBeforeSkew 2 |
Handling SignOut
With SSO configured, users can click the Sign Out options in UserVoice to log out of the system. This will log the users out of UserVoice, but they will still be logged in to the ADFS server with a valid authentication cookie. It is optional to configure the SignOut capability to also log users out of ADFS at the same time. If you wish to do this, follow the steps below:
- In ADFS, select the Relying Party Trust for UserVoice, right-click, and choose Properties…
- Under the Monitoring tab, make sure the Automatically update relying party option is unchecked. If checked, uncheck it and click Apply.
- Click the Endpoints tab. Add a new Endpoint, specify SAML Logout for the Endpoint type, POST for the binding, and enter a url similar to the following in the URL field: https://yourazureadfsserver.com/adfs/ls/?wa=wsignout1.0.
- In UserVoice administration, open the Edit User Authentication popup again. In the SSO REMOTE SIGNOUT URL textbox, enter the same exact url in step 3 above.














Thank you!
Your comment about the “-NotBeforeSkew 2” saved us hours!